WatchGuard has released patches for a critical-severity vulnerability in the Firebox firewalls, warning that it has been exploited in the wild.
Tracked as CVE-2025-14733 (CVSS score of 9.3), the zero-day is described as an out-of-bounds write issue affecting the Fireware OS’s iked process.
Successful exploitation of the flaw, WatchGuard says, could allow remote, unauthenticated attackers to execute arbitrary code on vulnerable devices.
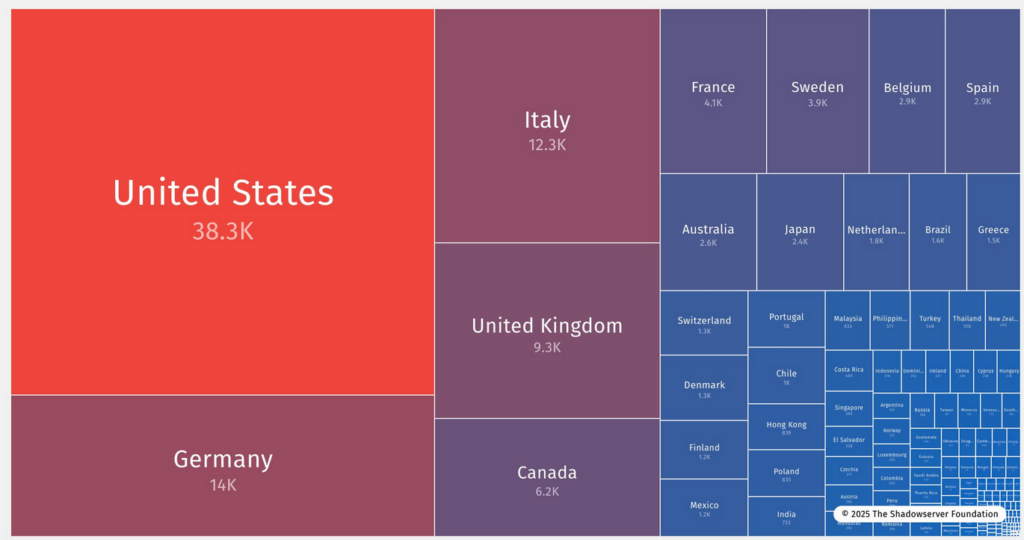
The Shadowserver Foundation has reported detecting roughly 125,000 IP addresses associated with WatchGuard firewalls affected by CVE-2025-14733, including nearly 40,000 located in the United States.
“This vulnerability affects both the mobile user VPN with IKEv2 and the branch office VPN using IKEv2 when configured with a dynamic gateway peer,” WatchGuard’s advisory reads.
According to the vendor, even Firebox instances that had the flawed configuration deleted could be vulnerable if they still have a branch office VPN to a static gateway peer configured.
“WatchGuard has observed threat actors actively attempting to exploit this vulnerability in the wild,” the company warns.
WatchGuard has provided indicators-of-attack (IoAs) to help defenders identify potential exploitation attempts against vulnerable Firebox appliances.
The exploited Firebox vulnerability impacts Fireware OS versions 11.x, 12.x, and 2025.x, and has been resolved in versions 2025.1.4, 12.11.6, 12.5.15, and 12.3.1_Update4 (B728352). No patch will be released for Fireware OS 11.x, which has reached end-of-life (EoL).
On Friday, the US cybersecurity agency CISA added CVE-2025-14733 to its Known Exploited Vulnerabilities (KEV) catalog, urging federal agencies to address it within a week.
Per Binding Operational Directive (BOD) 22-01, federal agencies have three weeks to resolve bugs newly added to KEV, but the severity of the exploited Firebox vulnerability demands expedited remediation, CISA suggests.
WatchGuard’s Firebox firewalls are designed to protect an organization’s environment from external threats, controlling all inbound and outbound network traffic.
Related: Critical WatchGuard Firebox Vulnerability Exploited in Attacks
Related: HPE Patches Critical Flaw in IT Infrastructure Management Software
Related: CISA Warns of Exploited Flaw in Asus Update Tool
Related: Gigabyte Rolls Out BIOS Updates to Remove Backdoor From Motherboards


